Overview
User objects (AKA People) represent individuals who have access to the Okta organization. Each user has a unique identifier, username in the email address format, and various attributes such as email, first name, last name, and status.
In OktaHound, users are represented as Okta_User nodes.
Edges
The tables below list edges defined by the OktaHound extension only. Additional edges to or from this node may be created by other extensions.
Inbound Edges
| Edge Type | Source Node Types | Traversable |
|---|
| Okta_ApiTokenFor | Okta_ApiToken | ✅ |
| Okta_Contains | Okta_Organization | ✅ |
| Okta_DeviceOf | Okta_Device | ❌ |
| Okta_GroupAdmin | Okta_User, Okta_Group, Okta_Application | ✅ |
| Okta_HelpDeskAdmin | Okta_User, Okta_Group, Okta_Application | ✅ |
| Okta_IdentityProviderFor | Okta_IdentityProvider | ✅ |
| Okta_InboundSSO | AZUser | ✅ |
| Okta_ManagerOf | Okta_User | ❌ |
| Okta_OrgAdmin | Okta_User, Okta_Group, Okta_Application | ✅ |
| Okta_OutboundSSO | Okta_User | ✅ |
| Okta_PasswordSync | Okta_User | ✅ |
| Okta_ReadPasswordUpdates | Okta_Application | ✅ |
| Okta_RealmContains | Okta_Realm | ✅ |
| Okta_ResetFactors | Okta_User, Okta_Group, Okta_Application | ✅ |
| Okta_ResetPassword | Okta_User, Okta_Group, Okta_Application | ✅ |
| Okta_ResourceSetContains | Okta_ResourceSet | ✅ |
| Okta_ScopedTo | Okta_RoleAssignment | ❌ |
| Okta_UserPull | Okta_Application | ❌ |
| Okta_UserSync | User, Okta_User, SNOW_User | ❌ |
Outbound Edges
| Edge Type | Destination Node Types | Traversable |
|---|
| Okta_AddMember | Okta_Group | ✅ |
| Okta_AppAdmin | Okta_Application, Okta_ApiServiceIntegration | ✅ |
| Okta_AppAssignment | Okta_Application | ❌ |
| Okta_CreatorOf | Okta_ApiServiceIntegration | ❌ |
| Okta_GroupAdmin | Okta_User, Okta_Group | ✅ |
| Okta_GroupMembershipAdmin | Okta_Group | ✅ |
| Okta_HasRole | Okta_Role, Okta_CustomRole | ❌ |
| Okta_HasRoleAssignment | Okta_RoleAssignment | ❌ |
| Okta_HelpDeskAdmin | Okta_User | ✅ |
| Okta_ManageApp | Okta_Application | ✅ |
| Okta_ManagerOf | Okta_User | ❌ |
| Okta_MemberOf | Okta_Group | ✅ |
| Okta_MobileAdmin | Okta_Device | ✅ |
| Okta_OrgAdmin | Okta_User, Okta_Group, Okta_Device | ✅ |
| Okta_OutboundSSO | AZUser, GH_User, jamf_Account, SNOW_User, Okta_User | ✅ |
| Okta_PasswordSync | Okta_User | ✅ |
| Okta_ReadClientSecret | Okta_ClientSecret | ✅ |
| Okta_ResetFactors | Okta_User | ✅ |
| Okta_ResetPassword | Okta_User | ✅ |
| Okta_SuperAdmin | Okta_Organization | ✅ |
| Okta_SWA | GH_User, jamf_Account, OP_User, SNOW_User | ❌ |
| Okta_UserPush | Okta_Application | ❌ |
| Okta_UserSync | Okta_User, User, AZUser, OP_User, SNOW_User | ❌ |
Properties
| Name | Source | Type | Description |
|---|
id | user.id | string | Unique user identifier. |
name | user.profile.login | string | Okta username/login. |
displayName | user.profile.displayName | string | User display name. |
oktaDomain | Collector context (non-API) | string | Okta organization domain where the user exists. |
login | user.profile.login | string | User login/UPN value. |
email | user.profile.email | string | Primary email address. |
firstName | user.profile.firstName | string | User first/given name. |
lastName | user.profile.lastName | string | User last/family name. |
title | user.profile.title | string | Job title from user profile when present. |
department | user.profile.department | string | Department value from user profile when present. |
city | user.profile.city | string | City/location value from user profile when present. |
state | user.profile.state | string | State/region value from user profile when present. |
countryCode | user.profile.countryCode | string | ISO-like country code from user profile when present. |
status | user.status | string | User lifecycle status. |
enabled | IsEnabled(user.status) | bool | Boolean status projection used by BloodHound. |
hasRoleAssignments | Calculated | bool | Indicates whether the user is assigned any administrative roles. |
credentialProviderName | user.credentials.provider.name | string | Authentication provider name for this user. |
credentialProviderType | user.credentials.provider.type | string | Authentication provider type for this user. |
managerId | user.profile.managerId | string | Manager identifier from user profile synchronization. |
activated | user.activated | datetime | Timestamp when the user account was activated. |
created | user.created | datetime | User creation timestamp. |
passwordChanged | user.passwordChanged | datetime | Timestamp when the password was last changed. |
lastLogin | user.lastLogin | datetime | Timestamp of the most recent successful login. |
lastUpdated | user.lastUpdated | datetime | Last profile/update timestamp. |
Sample Property Values
id: 00uw2sodn4ZPJJQyx697
name: john.doe@contoso.com
displayName: John Doe
oktaDomain: contoso.okta.com
login: john.doe@contoso.com
email: john.doe@contoso.com
firstName: John
lastName: Doe
title: Senior Identity Engineer
department: Security Engineering
city: Seattle
state: WA
countryCode: US
status: ACTIVE
enabled: true
hasRoleAssignments: false
credentialProviderName: OKTA
credentialProviderType: OKTA
managerId: joe.smith@contoso.com
created: 2025-10-03T18:45:57+00:00
activated: 2025-10-03T19:02:11+00:00
passwordChanged: 2026-01-12T14:27:03+00:00
lastLogin: 2026-02-20T09:41:55+00:00
lastUpdated: 2025-10-29T11:09:47+00:00
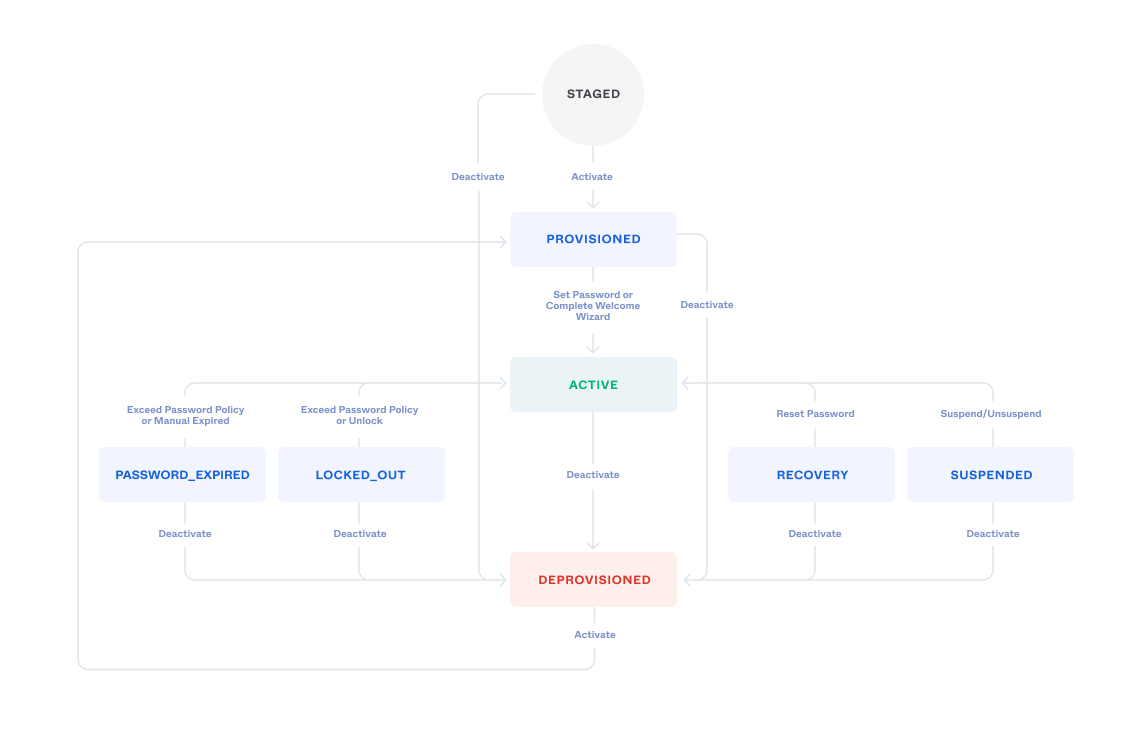
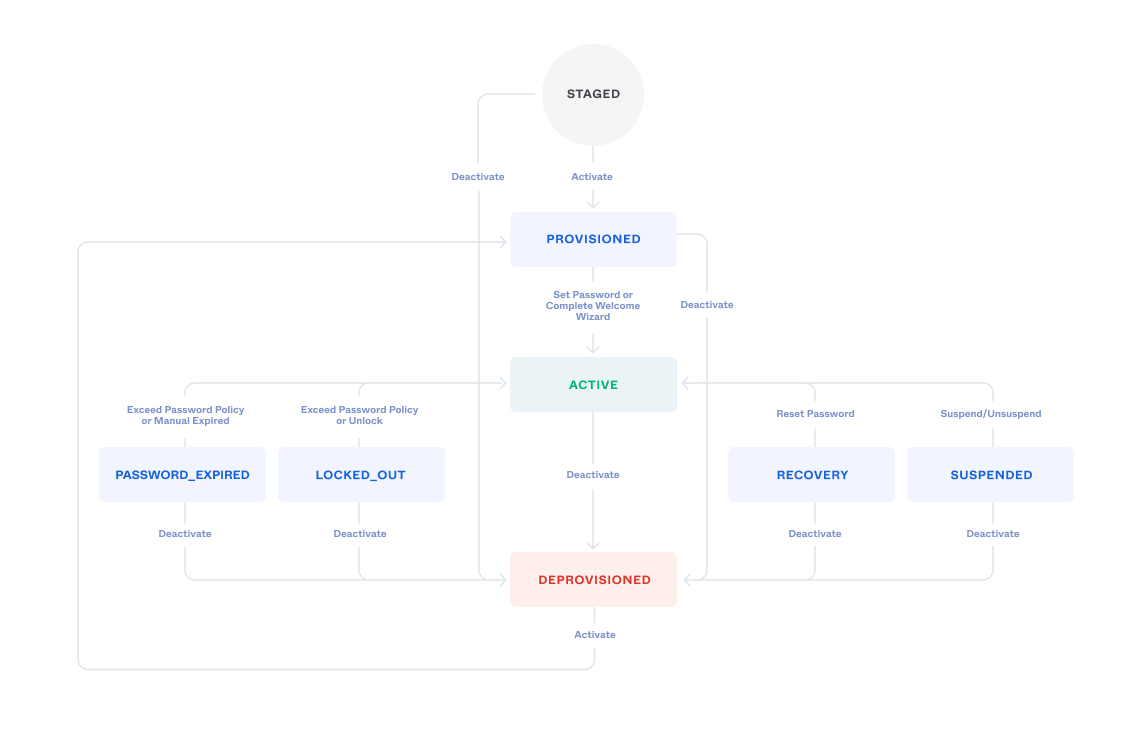
User Status
User status can have multiple values, as illustrated below:
 To simplify analysis in BloodHound, the
To simplify analysis in BloodHound, the OktaHound collector maps the Status attribute to the virtual boolean Enabled attribute as follows:
| Okta User Status | Enabled | Explanation |
|---|
| ACTIVE | ✅ | User can authenticate. |
| PASSWORD_EXPIRED | ✅ | User’s password has expired but can still authenticate. |
| LOCKED_OUT | ✅ | User is locked out but can still authenticate after unlocking. |
| PROVISIONED | ✅ | User is provisioned but cannot authenticate yet. |
| RECOVERY | ✅ | User is in recovery mode and cannot authenticate. |
| SUSPENDED | ❌ | User is suspended and cannot authenticate. |
| STAGED | ❌ | User is staged and cannot authenticate yet. |
| DEPROVISIONED | ❌ | User is deprovisioned and cannot authenticate. |
This mapping is a simplification and may not cover all edge cases.
Always refer to the actual Status attribute for precise user state information.
Authentication Factors
Okta supports various authentication factors for multi-factor authentication (MFA),
such as SMS, email, push notifications, and hardware tokens.
In case of mobile and desktop applications, these authentication factors are associated with the Device entities.
Other authentication factors, such as YubiKeys and Google Authenticator, are not represented as separate nodes in BloodHound,
but the number of enrolled factors is stored in the authenticationFactors attribute of the Okta_User nodes.
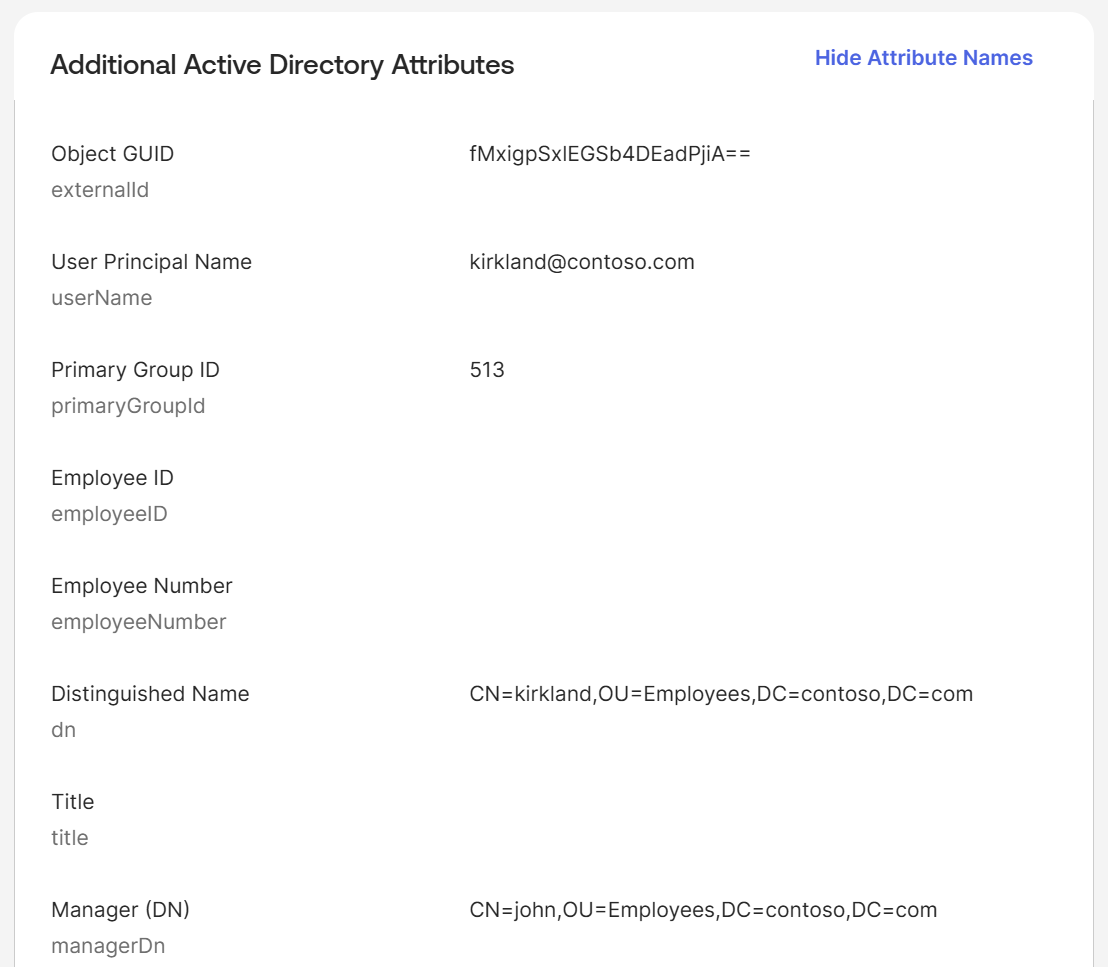
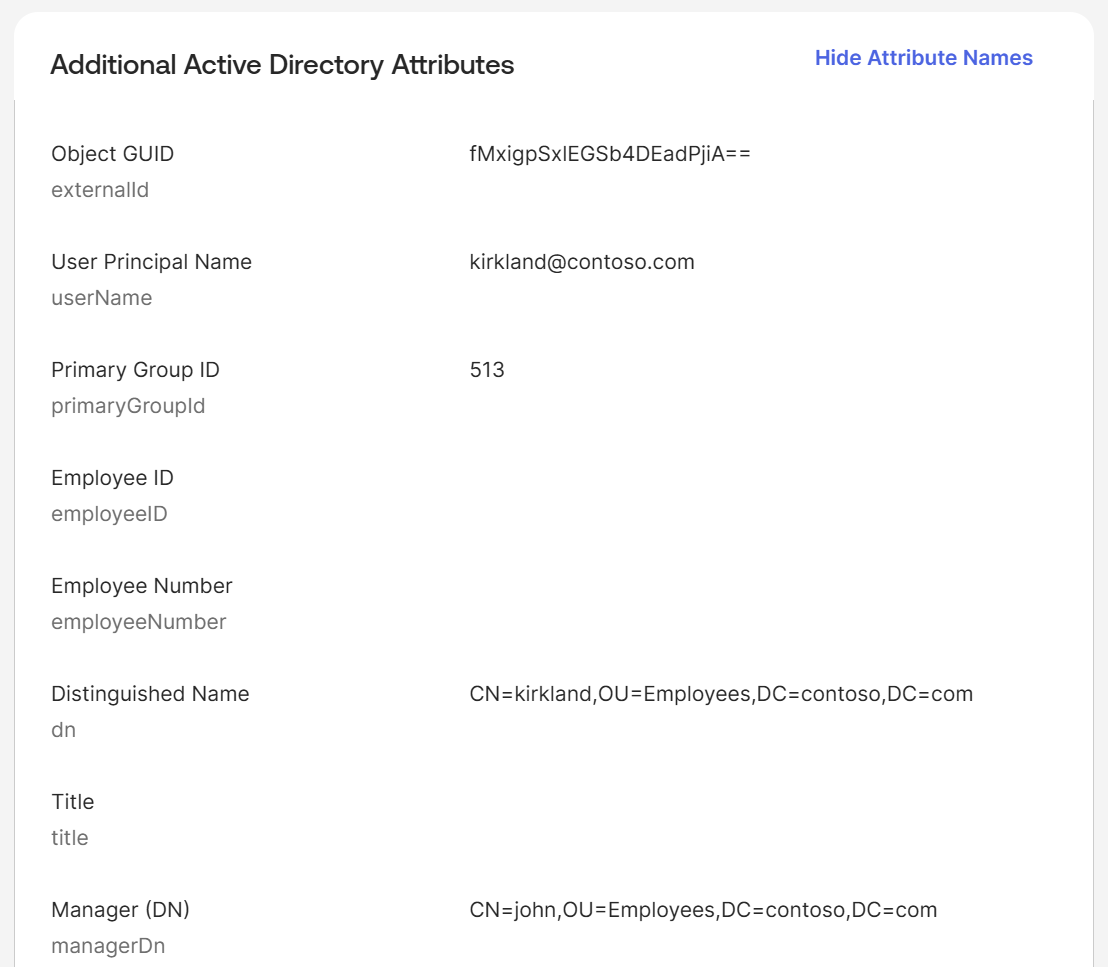
Synchronization with External Directories
Users can be synchronized from external directories such as Active Directory (AD) or LDAP. When synchronized, certain attributes may be mapped from the external directory to the Okta user profile.
 To simplify analysis in BloodHound, the
To simplify analysis in BloodHound, the