Open the Applications page
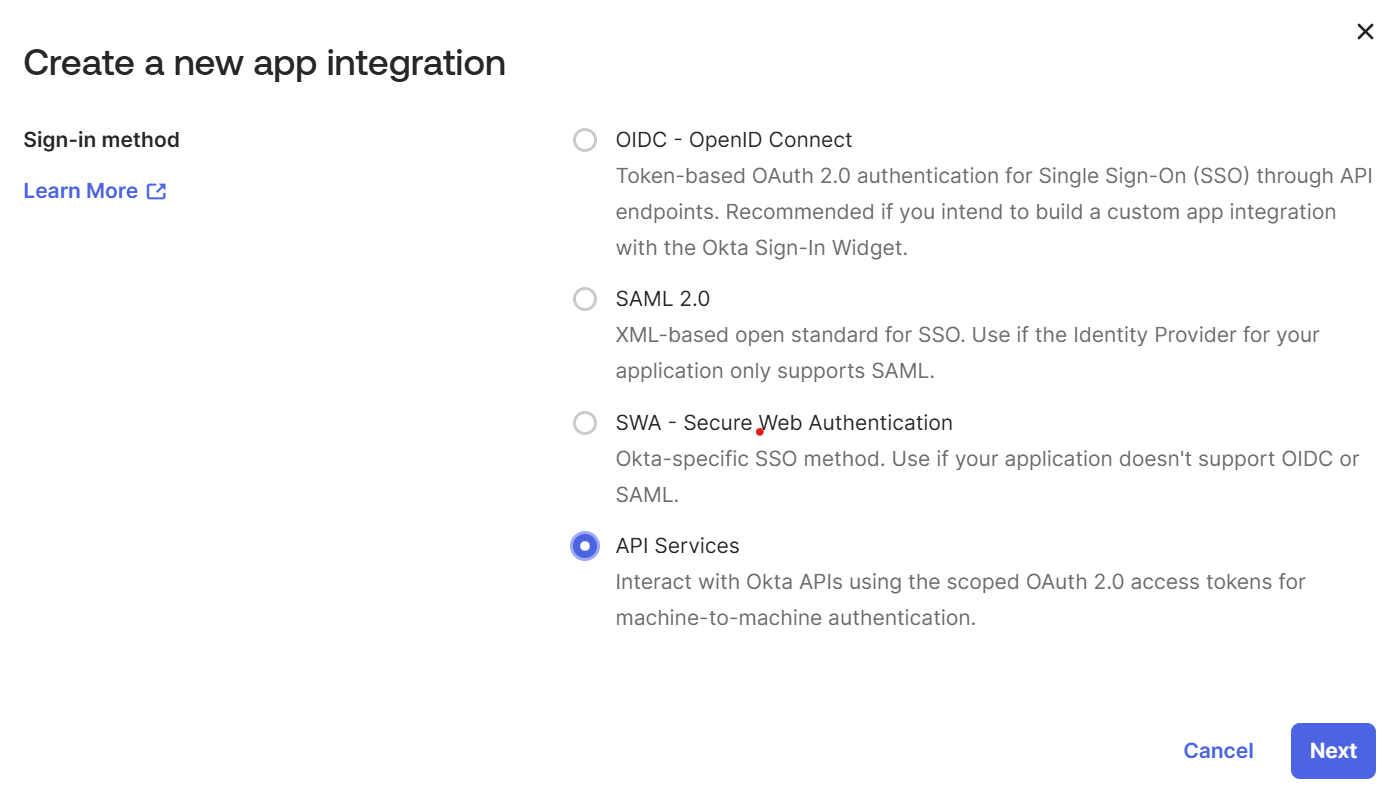
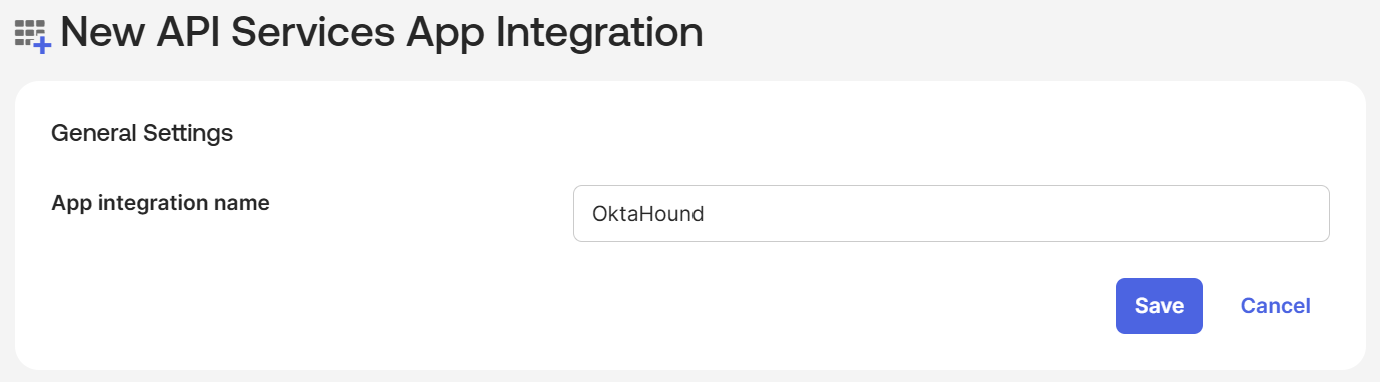
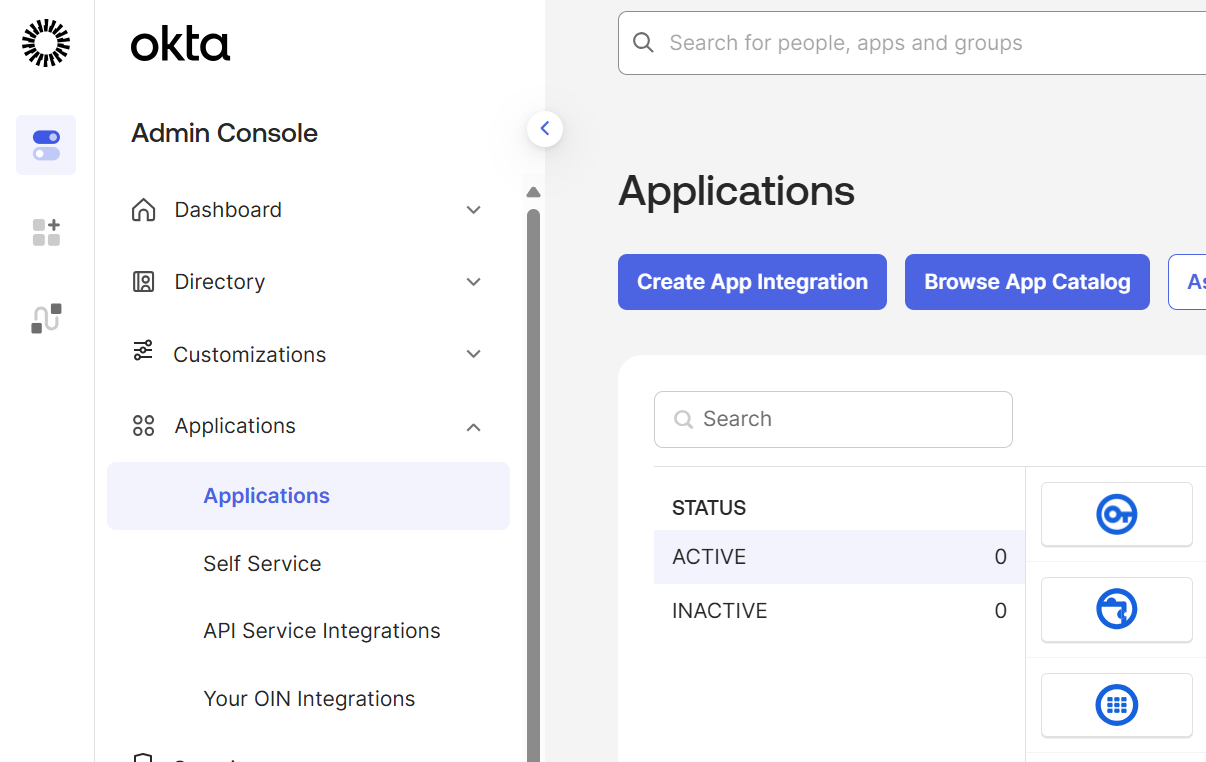
In the Okta Admin Console, navigate to Applications > Applications and click Create App Integration.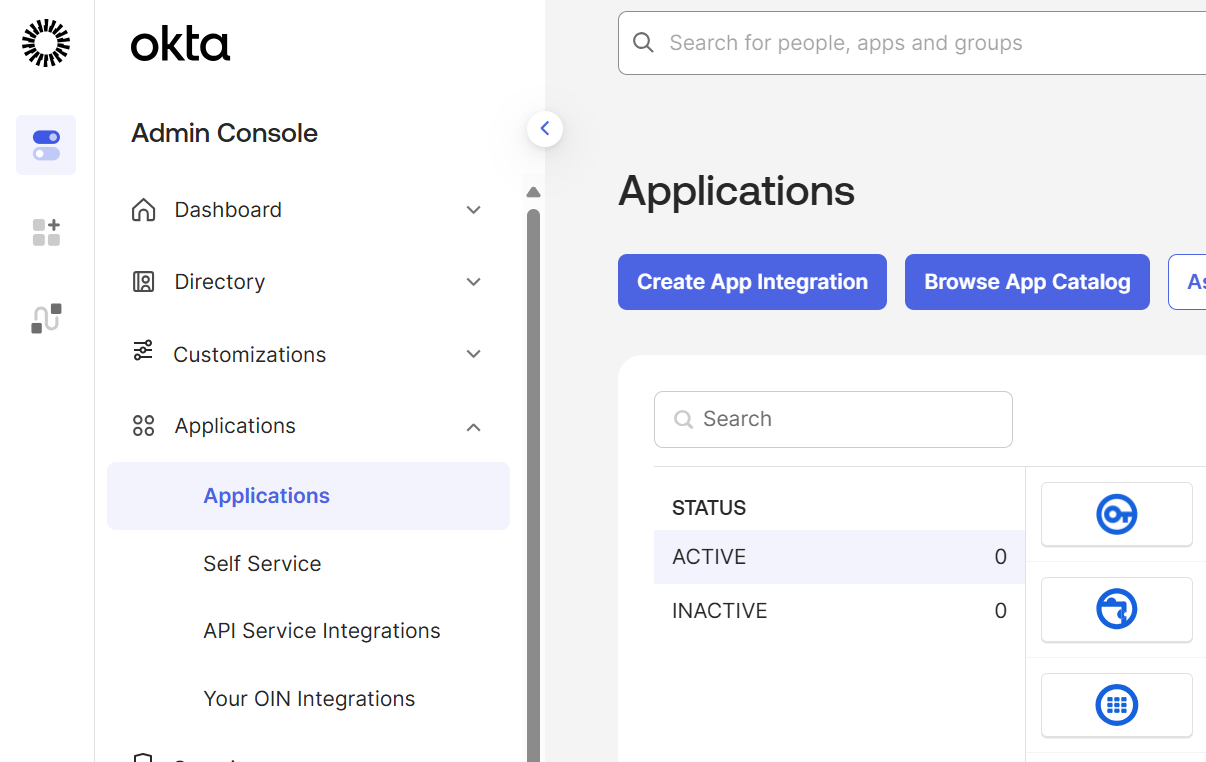
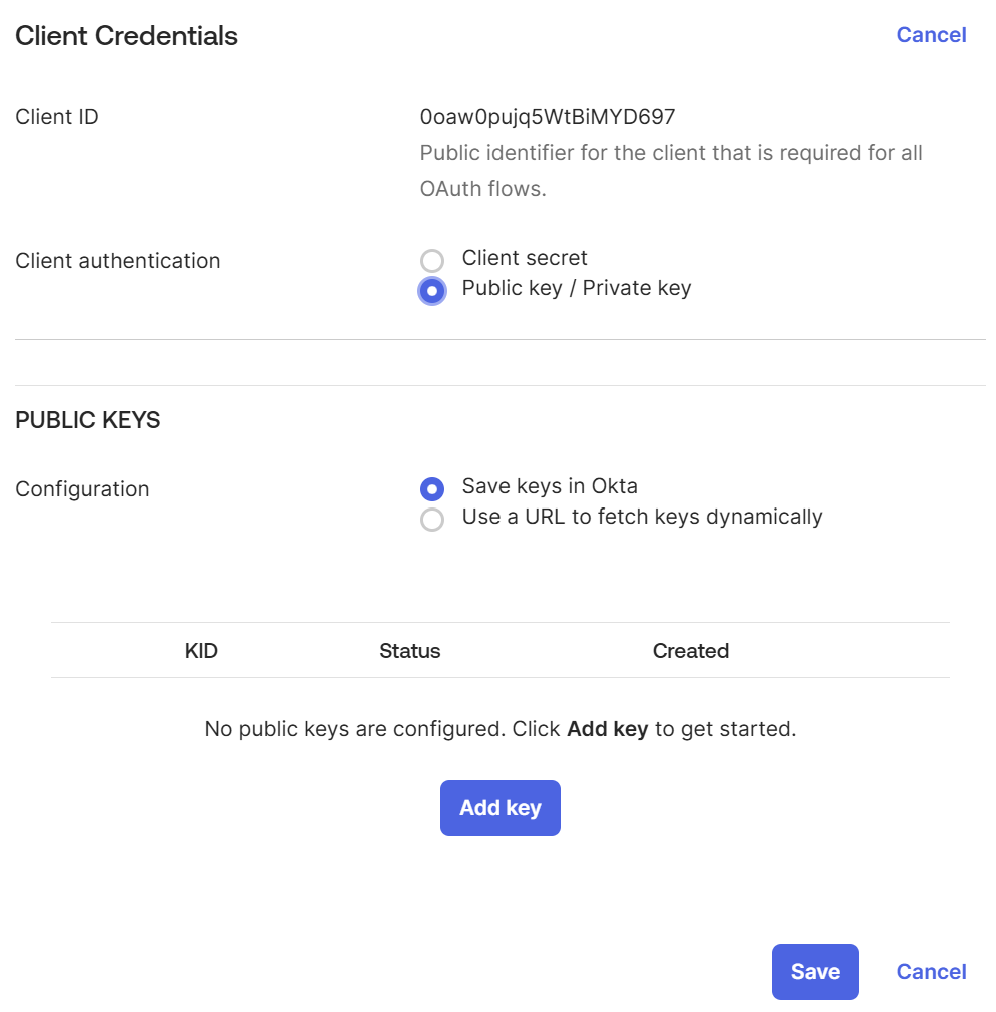
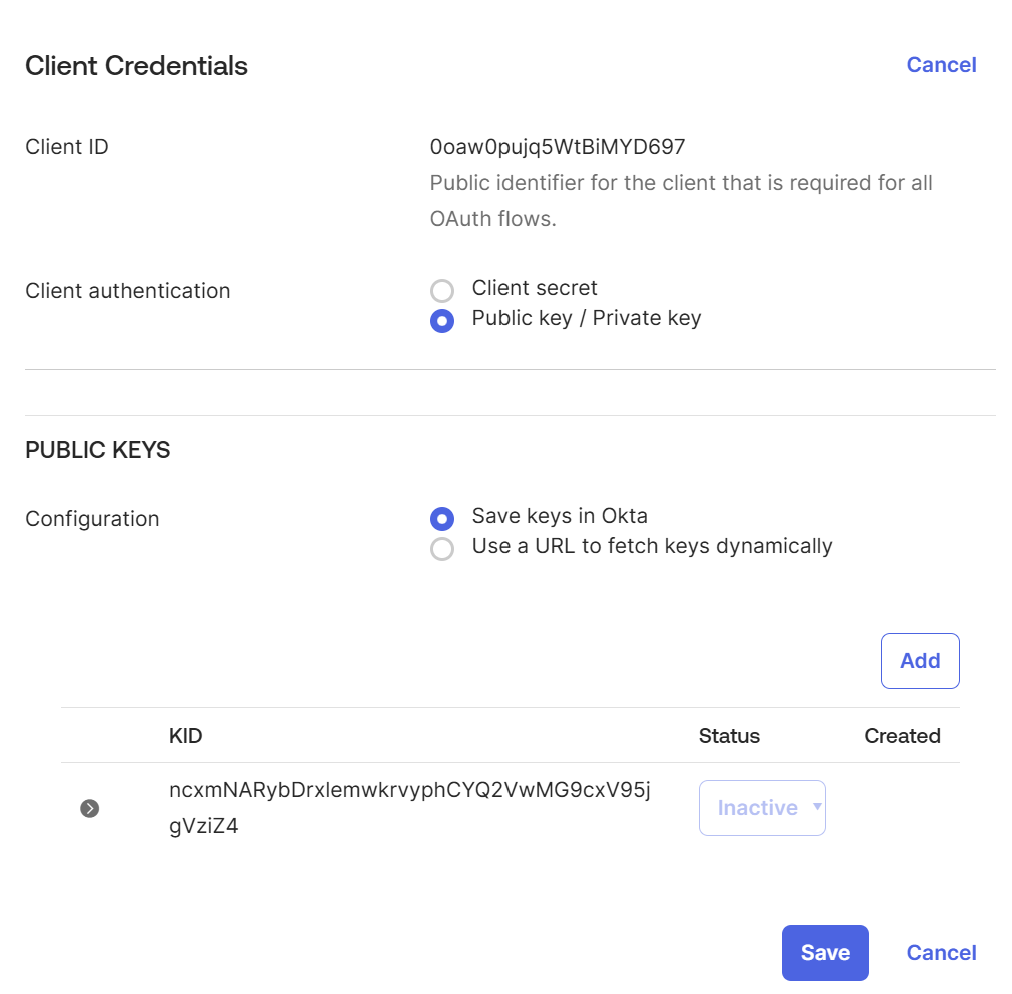
Configure public key authentication
After the application is created, you are taken to the General tab. Make a note of the newly created application’s Client ID for the 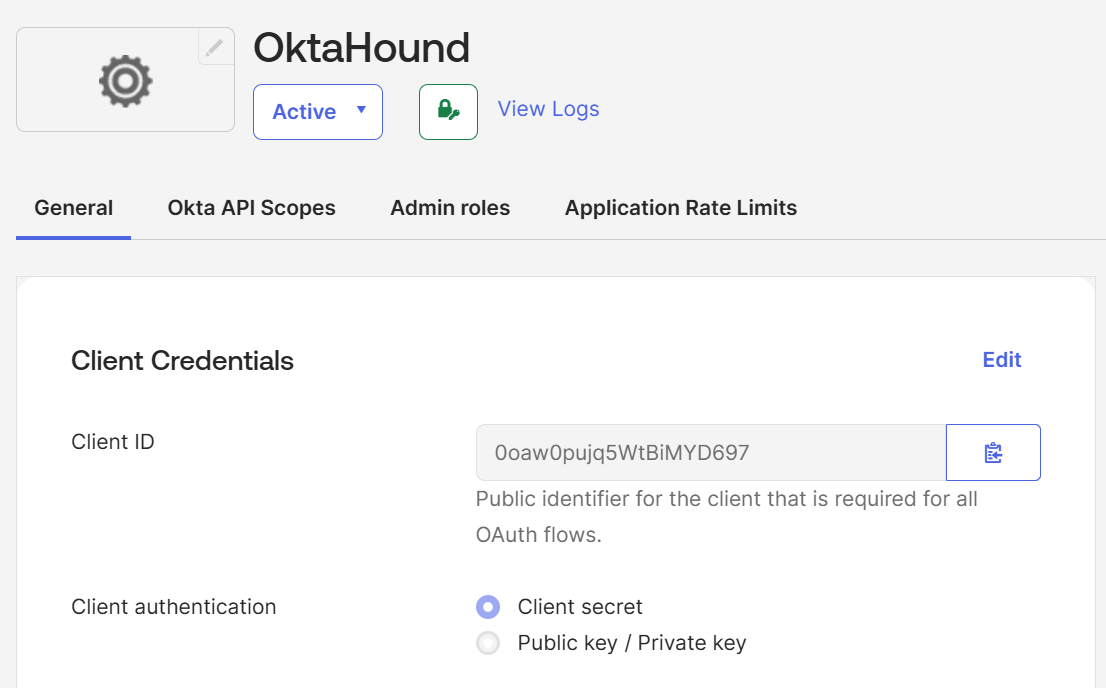
okta.yaml file.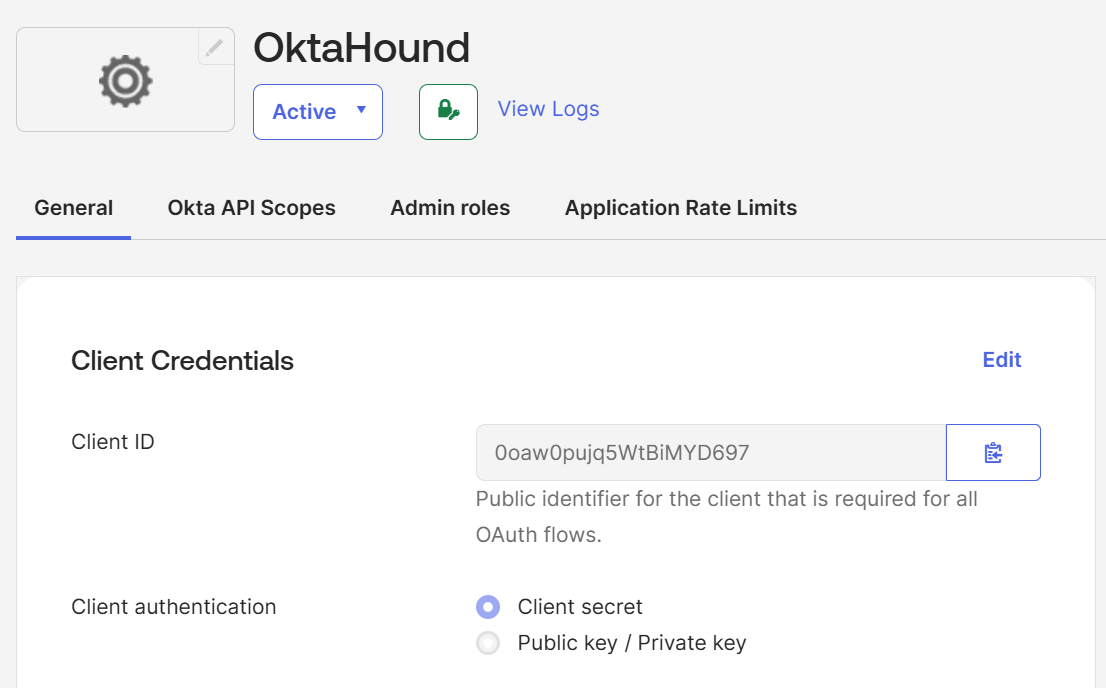
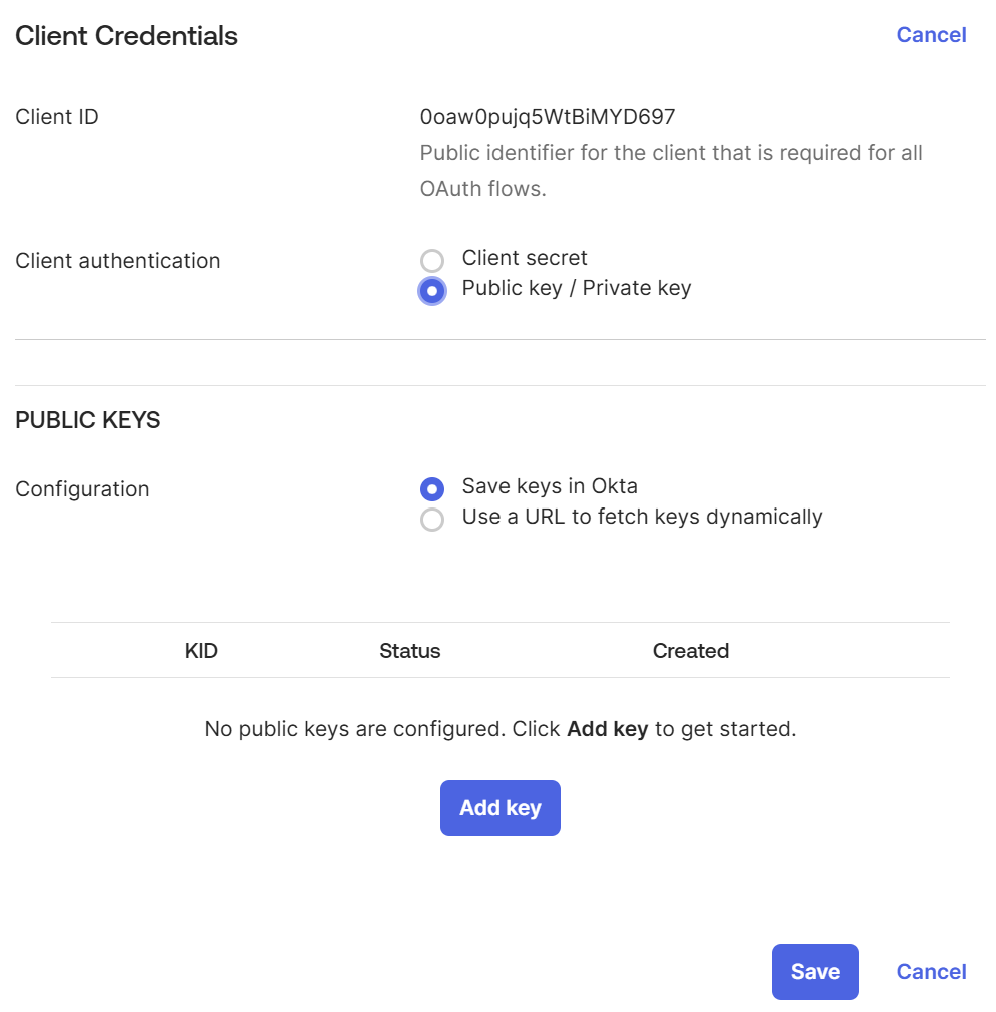
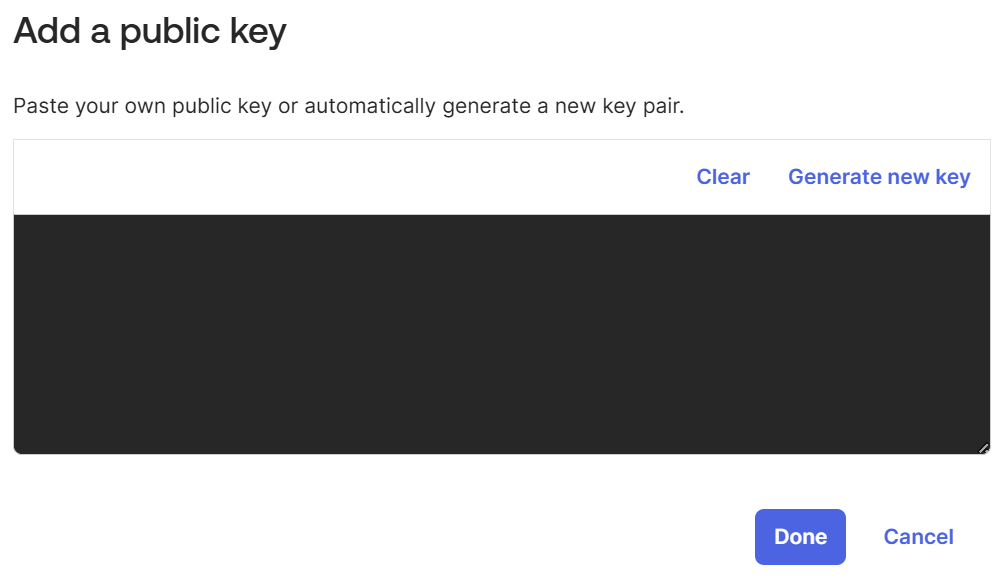
Generate a key pair
Under PUBLIC KEYS, click Add key, then click Generate new key.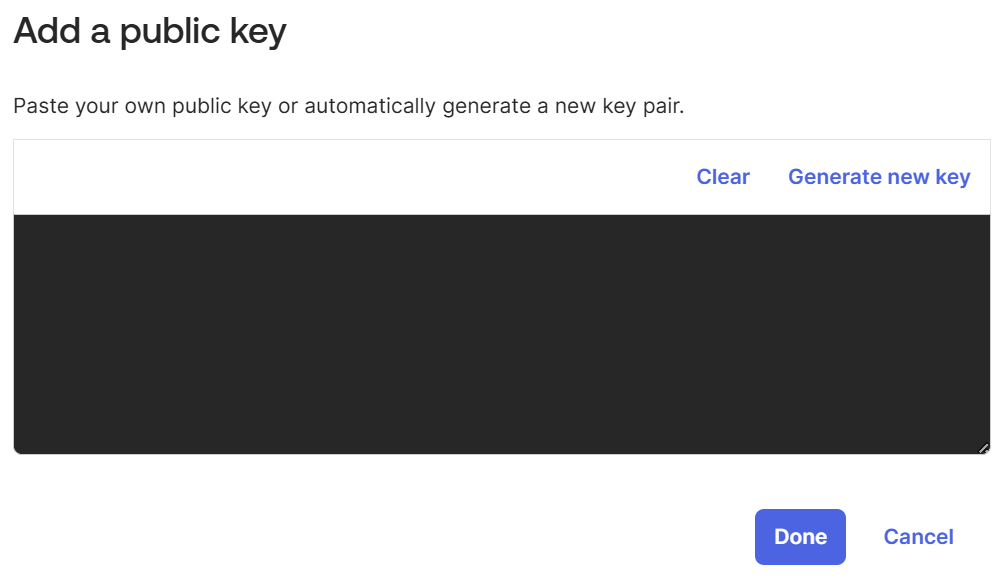
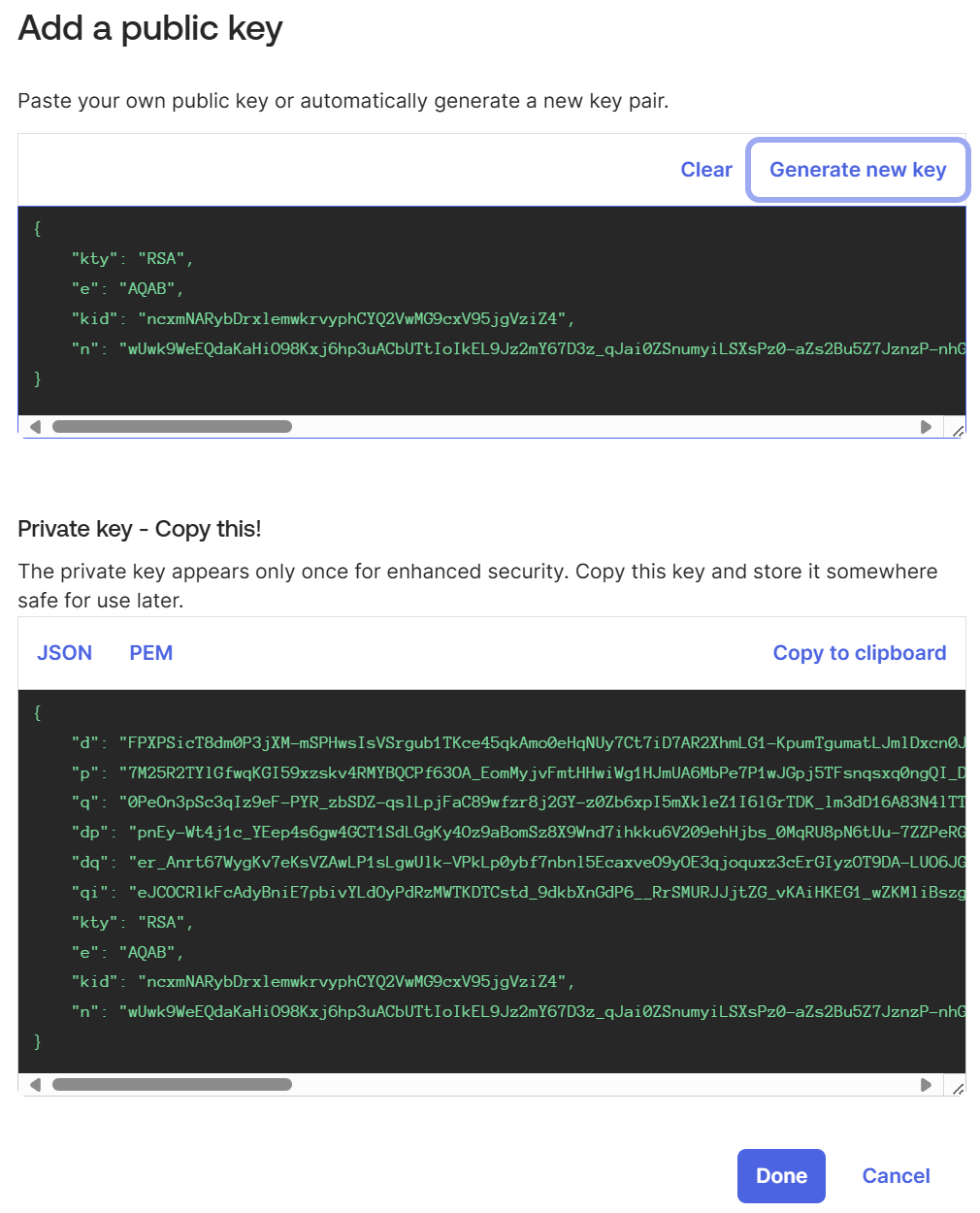
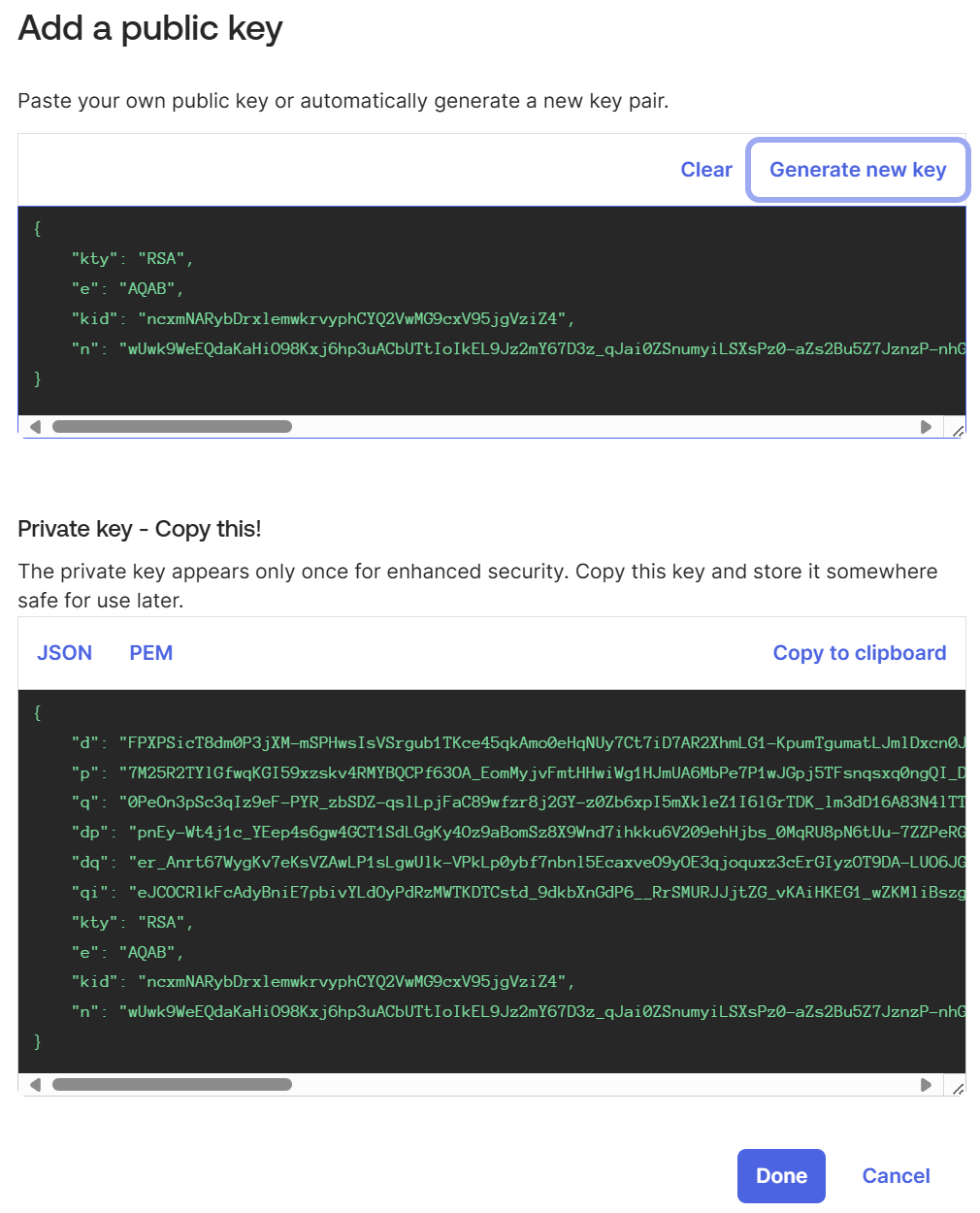
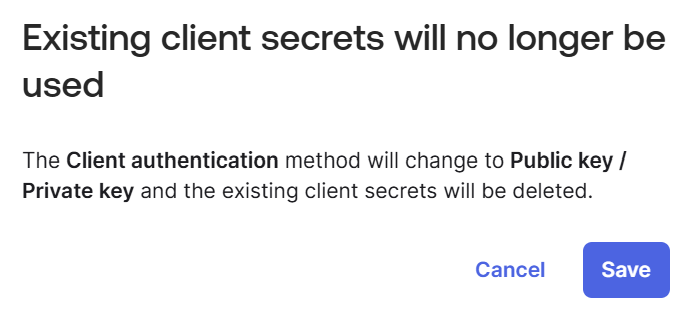
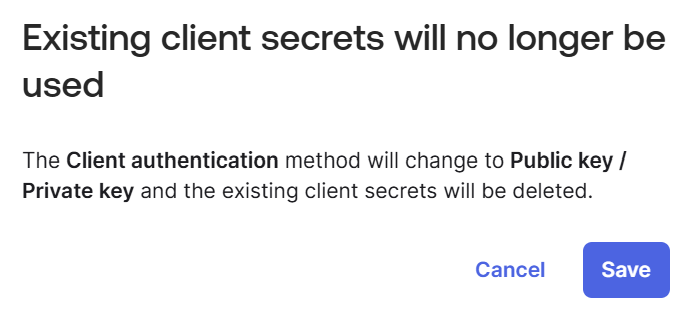
Save the credentials
Verify the key appears in the PUBLIC KEYS table, then click Save.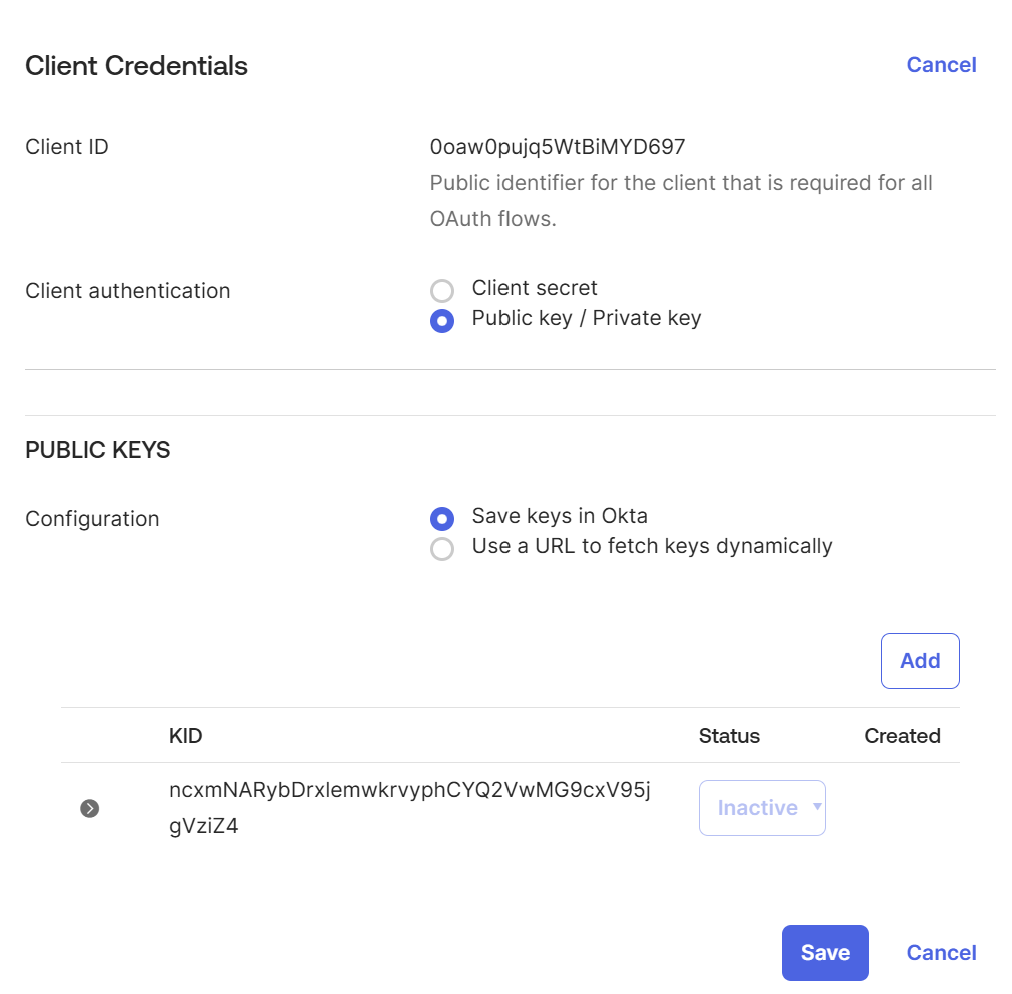
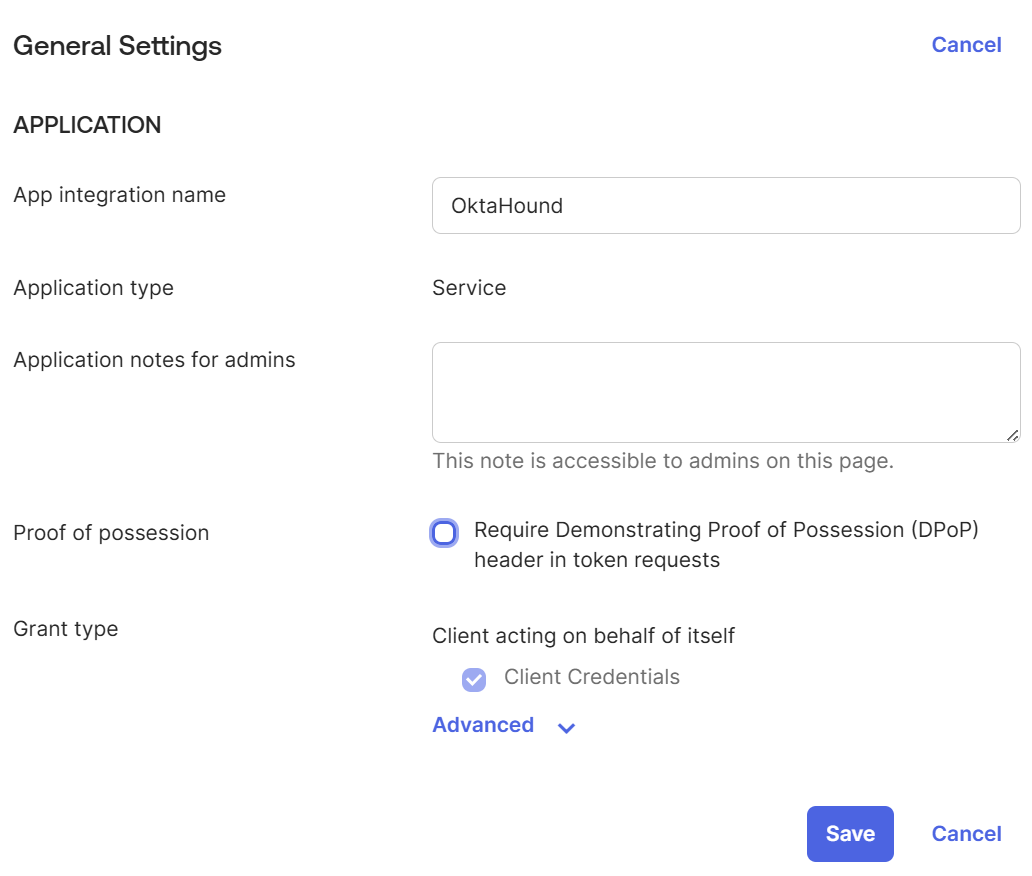
Disable DPoP requirement
Uncheck the Require Demonstrating of Proof of Possession (DPoP) option and click Save.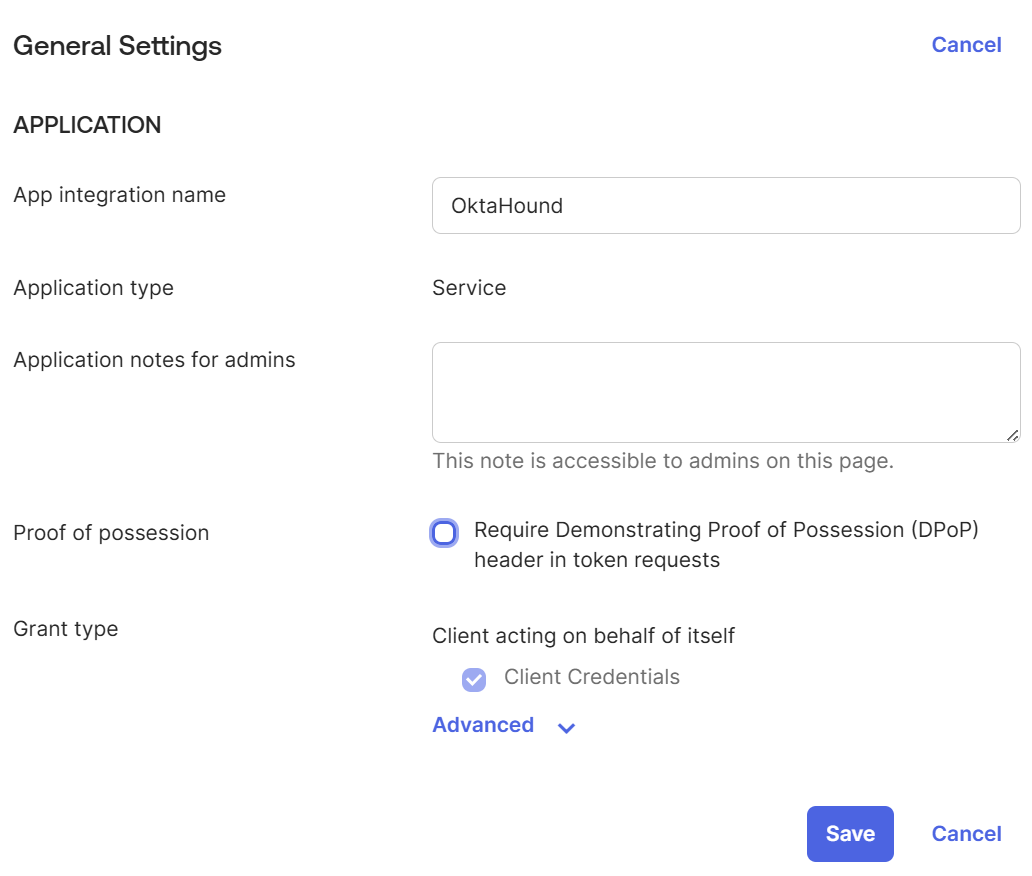
Grant OAuth 2.0 scopes
Navigate to the Okta API Scopes tab and grant the scopes required by OktaHound.The Okta application registration used by OktaHound requires the following OAuth 2.0 scopes for data collection to function correctly:
| OAuth 2.0 Scope | Description |
|---|---|
okta.orgs.read | Allows the app to read organization-specific details about your Okta organization. |
| okta.users.read | Allows the app to read the existing users’ profiles and credentials. |
| okta.groups.read | Allows the app to read information about groups and their members in your Okta organization. |
| okta.apps.read | Allows the app to read information about Apps in your Okta organization. |
okta.appGrants.read | Allows the app to read grants in your Okta organization. |
| okta.devices.read | Allows the app to read the existing device’s profile and search devices. |
okta.roles.read | Allows the app to read administrative role assignments for users in your Okta organization. |
okta.apiTokens.read | Allows the app to read API Tokens in your Okta organization. |
okta.agentPools.read | Allows the app to read agent pools in your Okta organization. |
okta.idps.read | Allows the app to read information about Identity Providers in your Okta organization. |
okta.authorizationServers.read | Allows the app to read information about Authorization Servers in your Okta organization. |
okta.oauthIntegrations.read | Allows the app to read API service Integration instances in your Okta organization. |
| okta.policies.read | Allows the app to read information about policies in your Okta organization. |
okta.features.read | Allows the app to read information about features in your Okta organization. |
| okta.realms.read | Allows the app to read the existing realms and their details. |
okta.realmAssignments.read | Allows a user to read realm assignments. |
okta.logs.read | Allows the app to read system log events in your Okta organization. |
Realm scopes are only available for tenants with the Okta Identity Governance add-on.
Assign admin role
Navigate to the Admin roles tab and assign the Super Administrator role.
Less privileged Okta roles currently cannot be used to read role assignments and OAuth 2.0 grants.
Due to the OAuth 2.0 scopes defined above, the OktaHound collector will not be able to modify any data in the Okta organization.