Documentation Index
Fetch the complete documentation index at: https://bloodhound.specterops.io/llms.txt
Use this file to discover all available pages before exploring further.
The other main product in Okta’s portfolio is Auth0 (previously known as Customer Identity Cloud). The Okta extension does not currently support Auth0.
Okta Attack Paths
Okta is an interesting target for attackers because it is widely used by organizations to manage access to cloud and on-premises applications. Compromising an Okta organization can provide attackers with access to a wide range of resources and data. Okta organizations are often secure by default, with MFA enforced for users and re-authentication required for sensitive administrative tasks. Okta also uses role-based access control (RBAC) to mitigate privilege escalation paths. As a result, many meaningful attack paths stem from misconfigurations, including excessive role assignments, weak authentication policies, insecure application integrations, and exposure of sensitive credentials. You should also account for users who are non-privileged in Okta but hold administrative access in connected applications, such as GitHub Enterprise Cloud or Amazon Web Services (AWS). Hybrid attack paths between on-premises Active Directory and Okta are also possible.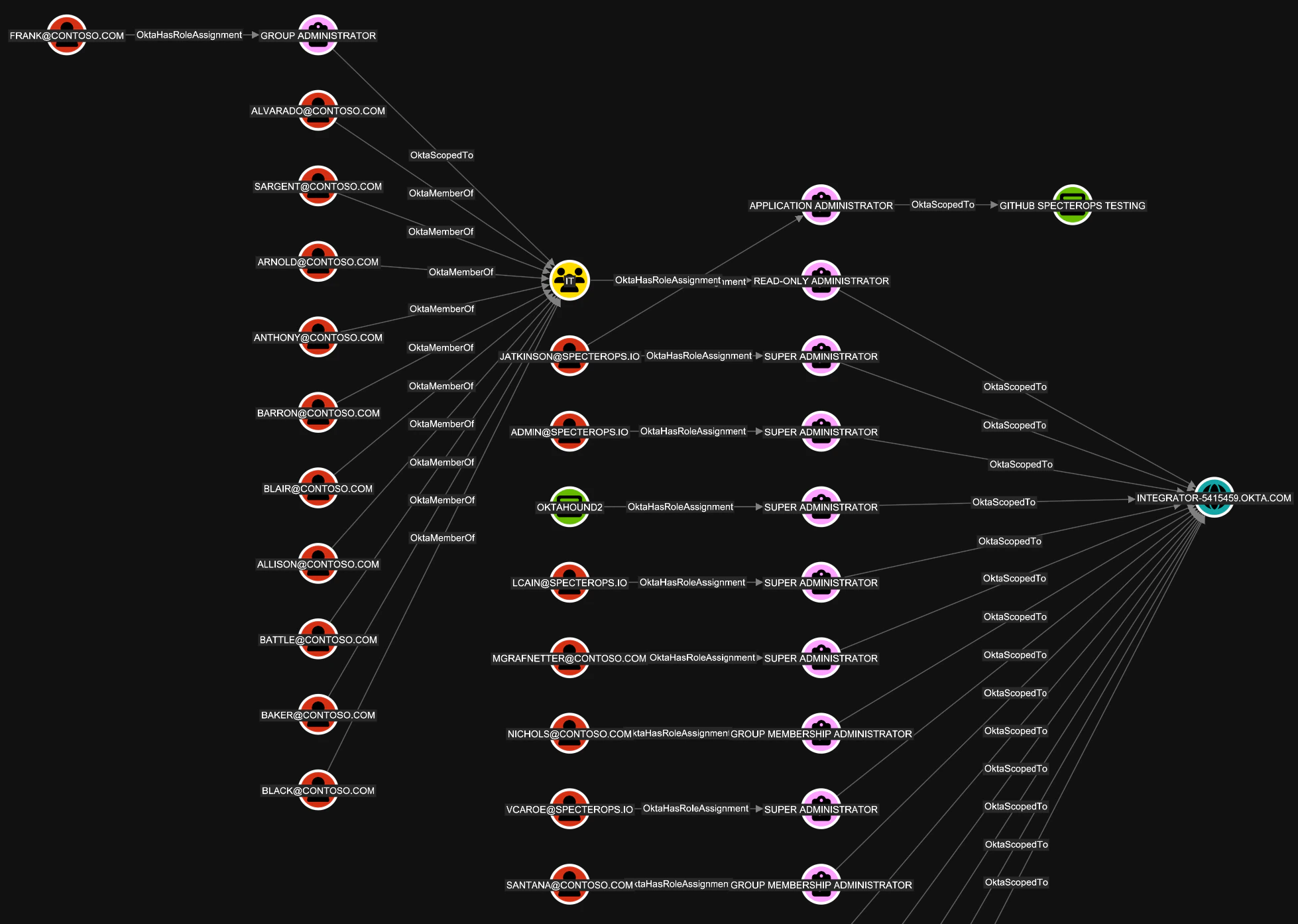
Our research on Okta attack paths is still ongoing. Interesting mappings to MITRE ATT&CK are available from Elastic.
Available Collectors
The Okta extension supports two collector paths:- OpenHound Okta collector: The SpecterOps-supported Okta collector. This is the primary documented path for collecting Okta data for BloodHound.
- OktaHound collector: An alternative Okta collector that also targets the Okta extension schema.
Okta Free Trial
Okta provides a free trial plan that you can use to test the majority of OktaHound features.References
The following blog posts provide insights into Okta attack vectors and techniques:- Michael Grafnetter (SpecterOps): Discovering Unexpected Okta Attack Paths with BloodHound
- Adam Chester (SpecterOps): Okta for Red Teamers
- Adam Chester (SpecterOps): Identity Providers for RedTeamers
- Eli Guy (XM Cyber): Attack Techniques in Okta - Part 1 - A (Really) Deep Dive into Okta Key Terms
- Eli Guy (XM Cyber): Attack Techniques in Okta - Part 2 - Okta RBAC Attacks
- Eli Guy (XM Cyber): Attack Techniques in Okta - Part 3 - From Okta to AWS Environments
- AppOmni: Okta PassBleed Risks - A Technical Overview
- Luke Jennings (PushSecurity): Abusing Okta’s SWA authentication
- David French (Elastic): Testing your Okta visibility and detection with Dorothy and Elastic Security
Research Tools
Here are some interesting GitHub repositories related to Okta security research:Community
Please join us in the#okta channel of the BloodHound Community Slack workspace if you want to chat about attack paths in Okta. You are also welcome to open an issue or pull request on GitHub.