The other main products in JAMF’s portfolio are JAMF Protect, JAMF Account, JAMF Now, and JAMF Connect. JamfHound does not currently support these products.
JAMF Pro Attack Paths
JAMF Pro is a highly valuable target for attackers in the modern enterprise. The privileged MDM actions required to administer Apple devices with JAMF Pro allow elevated access to local devices and complicates the jobs of EDRs and defensive teams trying to differentiate benign and malicious actions. Compromising a JAMF Pro tenant can provide attackers with a wide range of access to laterally move to Apple devices, exfiltrate information, lock or DOS devices, and more.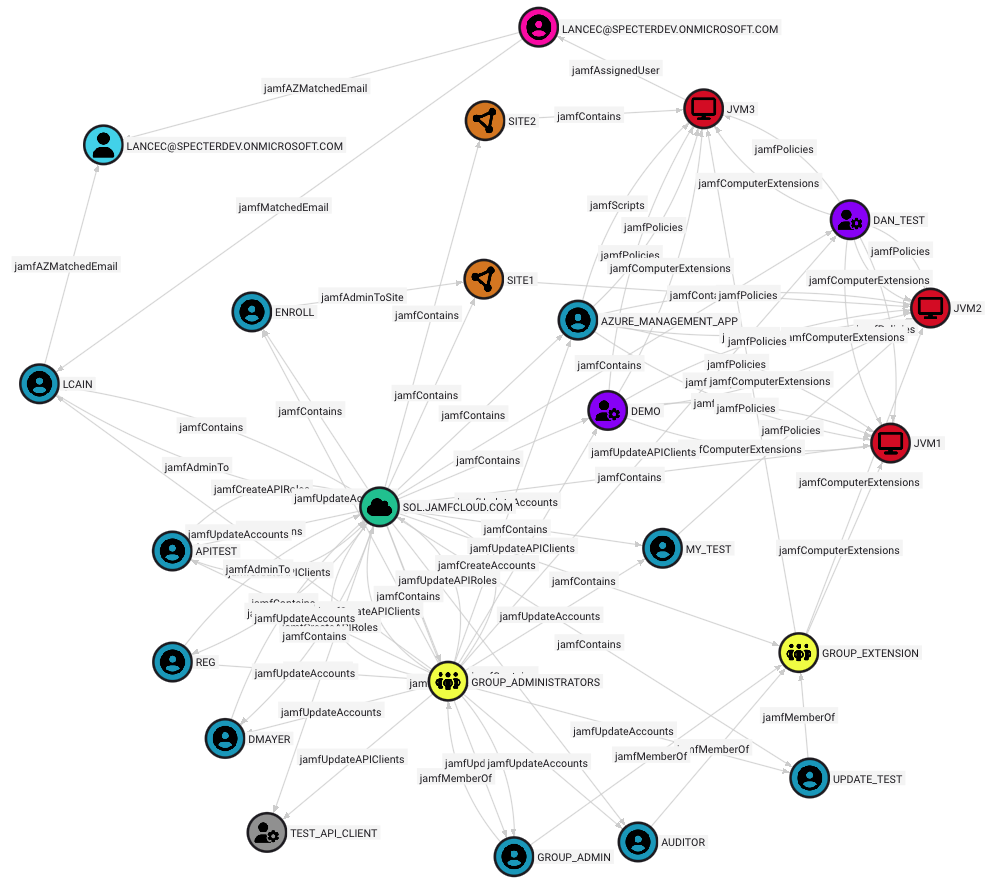
JAMF Pro Trial
JAMF Pro provides a free trial for organizations interested in testing their MDM capability.References
We recommend reading the following posts and pages to learn more about potential JAMF Pro attack vectors:- Lance Cain and Daniel Mayer (SpecterOps): Leveraging Jamf For Red Teaming in Enterprise Environments
- Video: Leveraging Jamf For Red Teaming in Enterprise Environments
- Calum Hall and Luke Roberts (GitHub): Come to the Dark Side, We Have Apples | Turning macOS Management Evil
- (1nf1n1ty): macOS Red Teaming | Abusing MDMs
Research Tools
Here are some interesting GitHub repositories related to JAMF Pro security research:Community
Please join us in the#jamf channel of the BloodHound Community Slack workspace if you want to chat about attack paths in JAMF or the usage of JamfHound. You are also welcome to open an issue or pull request on GitHub.