Documentation Index
Fetch the complete documentation index at: https://bloodhound.specterops.io/llms.txt
Use this file to discover all available pages before exploring further.
GitHub Attack Paths
GitHub is a highly valuable target for attackers in the modern enterprise. The privileged actions required to administer repositories, manage secrets, and control CI/CD pipelines allow elevated access to source code, cloud environments, and connected infrastructure, and complicate the jobs of defensive teams trying to differentiate benign and malicious actions. Compromising a GitHub organization can provide attackers with a wide range of access to laterally move across repositories, exfiltrate sensitive code and secrets, tamper with CI/CD pipelines, and pivot to connected cloud environments via OIDC federation.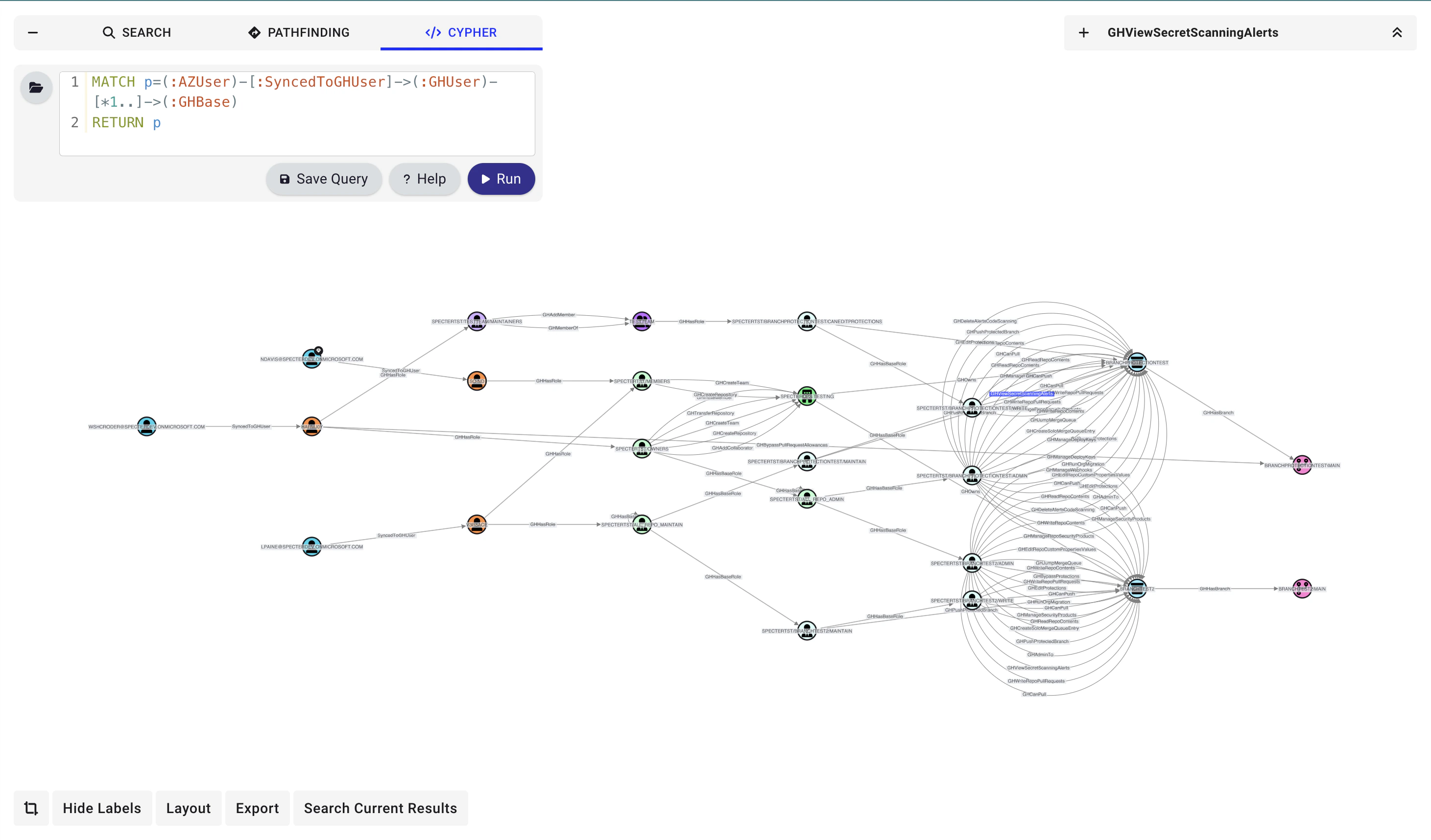
Our research on GitHub attack paths is still ongoing.
Available Collectors
The GitHub extension supports two collector paths:- OpenHound GitHub collector: The SpecterOps-supported GitHub collector. This is the primary documented path for collecting GitHub data for BloodHound.
- GitHound collector: An alternative GitHub collector that also targets the GitHub extension schema.
Community
Please join us in the#github-og channel of the BloodHound Community Slack workspace if you want to chat about attack paths in GitHub. You are also welcome to open an issue or pull request on GitHub.